In the financial sector, the stakes are incredibly high when it comes to securing digital transactions and protecting customer data. Spoofing attacks, where an unauthorized individual tries to gain access by impersonating someone else, are a growing concern. European Union Agency for Cybersecurity (ENISA) outlines five key categories of countermeasures for remote identity proofing, which are particularly relevant for financial entities aiming to fortify their defenses against spoofing attacks. This article delves into these five categories, emphasizing their application in the banking and financial sector.
Before diving into the specifics, it's important to note that achieving an entirely foolproof system is virtually impossible. The goal is to make the cost and complexity of executing a spoofing attack far outweigh any potential gains. This involves a careful balance between the effectiveness of security measures and the usability of the system, especially in high-stakes environments like banking.
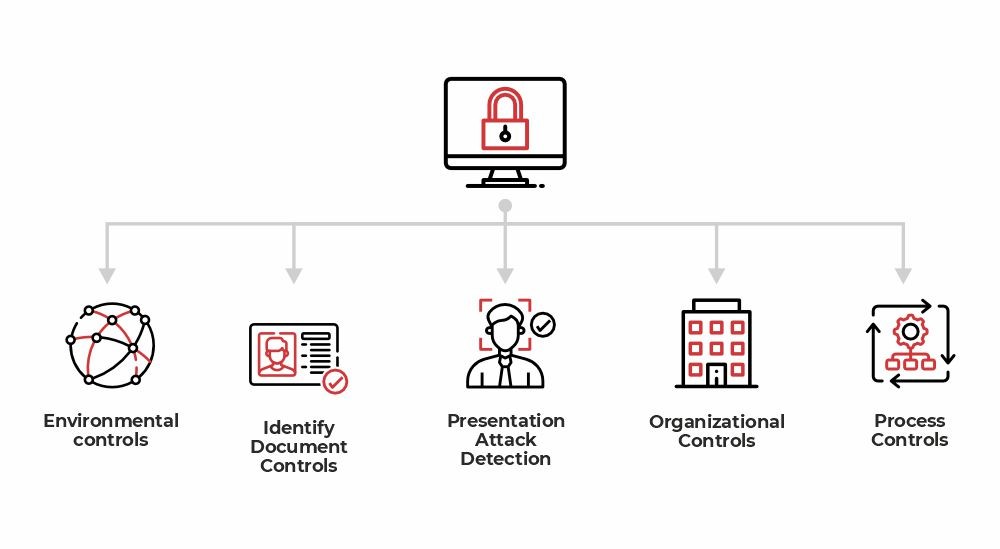
1. Environmental Controls
For banks, the environmental controls should extend beyond just the software and hardware used for identity verification. They should also encompass the network security protocols and firewall settings that protect against unauthorized access. Ensuring that the digital environment is secure can significantly reduce the risk of spoofing attacks.
2. Identity Document Controls
Financial institutions often require multiple forms of identification for transactions. Advanced algorithms can be employed to scrutinize the authenticity and validity of these documents. This is crucial for preventing identity theft, a common precursor to spoofing attacks. Features like hologram checks and real-time database cross-referencing can add an extra layer of security.
3. Presentation Attack Detection
In a sector that increasingly relies on biometric verification, banks must invest in cutting-edge presentation attack detection technologies. These systems can differentiate between a real human face and a photo or mask, thereby preventing spoofing attempts that use fake facial recognition data.
4. Organizational Controls
Banks and financial institutions should have stringent organizational controls, including regular security audits and specialized training programs for employees. A dedicated fraud detection unit can monitor for unusual activities that may signal a spoofing attack, allowing for immediate action.
5. Process Controls
The actual steps involved in identity verification should be rigorously defined and monitored. Multi-factor authentication, time-sensitive codes, and other process controls can be particularly effective in preventing spoofing. These measures not only secure the transaction but also provide a seamless experience for legitimate users.
Spoofing attacks pose a significant risk to banks and financial institutions, where the consequences of a security breach can be catastrophic. While no system can guarantee 100% security, a well-balanced and multi-faceted approach can make spoofing attacks highly impractical, thereby safeguarding both the institution and its customers.